SOC 2 Certification for Small and Medium-sized Enterprises
As an independent third-party service auditor, we can help SMEs prepare for SOC 2 report attestation, including identification of key areas necessary for compliance, perform control testing and sign the audit opinion accordingly.
American Institute of Certified Public Accountants (AICPA) Membership
Addressing the unique needs of growing companies
At E Secure 360, we have a deep understanding of growing businesses and are familiar with the unique regulatory issues they face. Business owners and entrepreneurs demand an all-rounded adviser and trusted business partner who can provide relevant and timely advice at a strategic, management or board level to help their businesses grow, develop and demonstrate compliance.
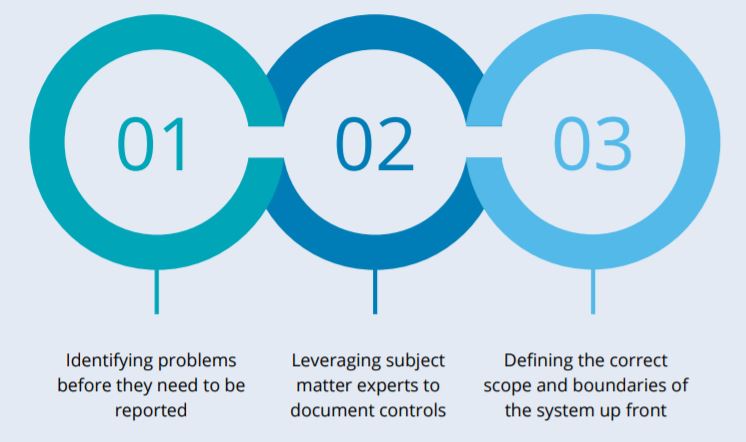
With our flexible work plans and structured walkthrough processes, we tailor our approach that works for you – reducing the effort needed to gather required information while also helping you and your staff gain a clearer understanding of the SOC 2 requirements.
Driving profitable growth through strategic compliance management

How E Secure 360 supports SMB growth and compliance
E Secure 360’s proprietary tools and methodologies, combined with deep industry and technical experience, our standard pricing model for SMBs help your business management strategies into a sustained source of competitive advantage to help you outperform your peers and improve your overall market value.
E Secure 360 is recognized as one of the market leaders in security, privacy, and internal control services. Our SOC 2 report can give organizations a competitive advantage and open up their market to new billion-dollar industries.
The compliance lifecycle and E Secure 360 specialised services
SMEs are normally profiled based on the parameters of their financials or number of employees and doing things cheaper, faster and better, is a necessity. Managing risks intelligently is key to having a positive outcome.
We work with our clients to identify value-added business insights, provide recommendations for improvement throughout the engagement, and ensure a smooth and consistent process. E Secure 360 methodology for preparing and delivering SOC 2 reports follows a phased approach, customized to meet the specific business needs of our clients that provide cloud computing, blockchain and IT managed services.









