Web Application Penetration Testing
Our Application Penetration Testing and Security Assessment services can be employed to test your
custom web applications as well as standard applications like antivirus, embedded applications, games, and other system applications
Uncover vulnerabilities scanners cannot find
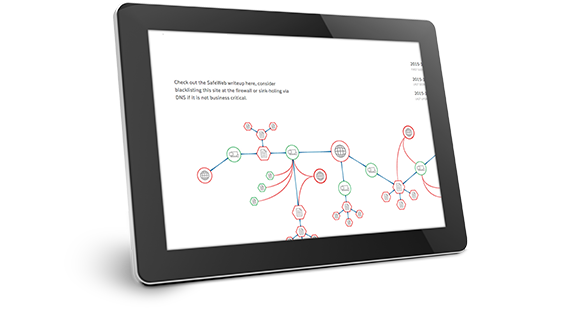
Ensure application security by uncovering vulnerabilities such as business logic, and authorization and authentication flaws, which can only be found by manual testing. During application testing engagements, our consultants pursue the following goals:
- Explore weakness as a hacker & reveal security flaws resulting from implementation errors
- Assess application security versus attacks via multiple techniques
- Identify security design flaws and demonstrate the potential consequences
- Expose weaknesses stemming from application relationship to the the IT infrastructure
- Increase end-user confidence in the application’s overall security
Embed security into your application development lifecycle
To reduce your risk of a compromise and gain the trust of your customers, we can test your applications before and after they go to market. E Secure 360 has been building and refining methodologies to assess the security posture of applications built across the varying platforms and languages used in decades worth of development. These methodologies map to proven OWASP standards while also accommodating the discovery of issues particular to your web applications, web services, or thick client applications. Key benefits of our Web Application penetration test include:
- Gain real-world insight into your vulnerabilities
- Find any loopholes that could lead to the theft of sensitive data
- Comply with requirements of PCI DSS, GDPR, HIPAA, and ISO 27001 on Application security
- Identify security issues related to business logic and work flow patterns
- Comprehensive report that includes proof of concept for vulnerabilities and video evidence demonstrations
Research-driven methodologies that incorporate industry security standards
Our Web Application Penetration test ensures consistency and repeatability to minimize the risk to systems under test and to cover all the vital areas








